Today I will tell you how you can allow or block a program to be connected to the internet, from Control Panel but first we should know :-
Why do you need to block a program to be connected to the Internet?
Well, answer is so simple, "Because I dont want to update this Program anymore from its server on the Internet." In other cases, when you crack a Software or a PC Game or download a crack for your favorite PC Game, most of the times you will see a *.*txt file inside that Crack folder giving you instructions how to install that Game. And when you see "Block this game to be connected to the Internet from Control Panel > Windows Firewall.
If you are using your PC at Home for playing games in free time, very little chances you have installed any Antivirus software in your PC or if you are using a paid version of Antivirus software, you will open it mostly once in a week. But I would suggest you should open and read what's inside settings or inside advance settings, but never try to change any settings you are not familiar of.
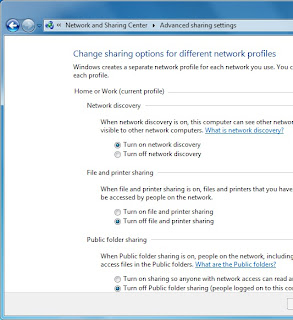
If you look closer inside your Antivirus settings you will find the exact settings of allowing or blocking a program from Internet. But here I am showing your the same settings from Control Panel, in case you don't have any Antivirus Installed.
A look at my PC settings first, I am using Windows 7 Ultimate with AVG Free Antivirus Installed. Don't worry if you are using Windows 8 or 8.1 or any version of Windows 7, all you need to do is to find where that Control Panel is...
Follow me if you are using Windows 7.
1. Click Start
2. Type the word "Allow", you will see "Allow a program through Windows Firewall" on the top, press Enter or click on it.
NOTE: If you are using Windows 8 you can still find this settings under Control Panel.
 3. This setting will be opened, where you can easily check the boxes to allow or block a program through Windows Firewall. In case you aren't able to click the boxes, make sure you clicked the "Change Settings" button (showing on the top right in the picture).
3. This setting will be opened, where you can easily check the boxes to allow or block a program through Windows Firewall. In case you aren't able to click the boxes, make sure you clicked the "Change Settings" button (showing on the top right in the picture).This is all done, once you blocked a program through Windows Firewall it will not be able to connect to internet anymore, and will not be updated.
As I mentioned before, you can also block a program through your Antivirus settings, if you have one.
Thanks for reading, your feedback will be appreciated.